What if your healthcare backup is available when you need it, but the data inside it cannot be trusted to restore cleanly?
That is where real recovery risk begins. In healthcare, a backup failure can delay access to patient records, interrupt scheduling, affect billing, and slow clinical operations at the exact moment systems need to come back online. The problem is not always missing backup data. Sometimes the bigger issue is whether the restore point is still safe, intact, and usable after ransomware, deletion, or hidden corruption.
This is why healthcare organizations are putting more focus on backup integrity, recovery trust, and resilience under pressure. CISA continues to recommend backups that are encrypted, immutable or offline, and regularly tested for restoration.
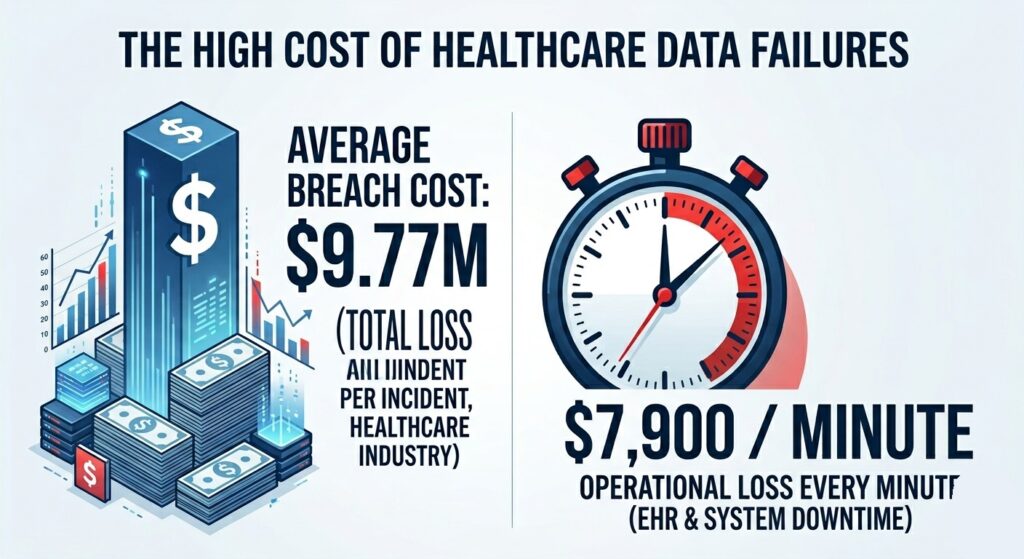
The financial stakes of healthcare recovery are exceptionally high, making reliable backups a fiscal necessity.
Healthcare also remains the costliest industry for data breaches, averaging $9.77 million per breach in IBM’s 2024 analysis, while EHR and internal-system downtime can cost about $7,900 per minute. [source]
To understand why this matters, start with what makes a backup immutable and why that distinction matters in healthcare recovery planning.
What are Immutable Backups in Healthcare?
An immutable backup is a backup copy that cannot be changed, deleted, or overwritten during a defined retention period. In healthcare, that matters because EHR data, patient records, imaging, and other critical systems may need to be restored after ransomware, accidental deletion, or system failure.
How are Immutable Backups Different From Standard Backups?
A standard backup creates a copy of data. An immutable backup creates that copy and then protects it from alteration for a set period of time. This makes it harder for attackers, administrators, or automated processes to erase or modify the backup after it has been created.
That distinction is important in healthcare because a backup can still exist while becoming unreliable as a restore source. If a restore point is deleted, encrypted, or altered before recovery begins, the organization may still face extended downtime.
How is Backup Immutability Enforced?
Immutability is usually enforced through technical controls such as retention locking, object lock, or WORM-style storage behavior. The method can vary by platform, but the goal remains the same: preserve a backup copy in a fixed state until the retention period ends.
Why Immutability Supports Trusted Recovery
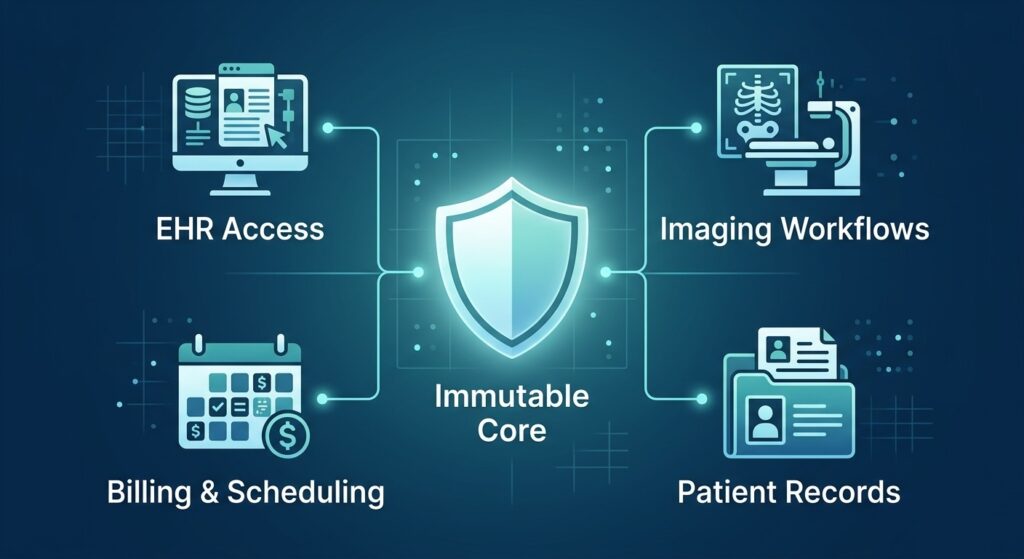
Immutable backups provide the foundation for recovering all facets of clinical and administrative operations.
Healthcare organizations depend on timely access to accurate data. When a backup is protected from change, the organization has a better chance of recovering from a trusted point instead of discovering too late that the backup itself was compromised. That is especially important for environments that rely on EHR access, imaging systems, scheduling platforms, and billing records to keep daily operations moving.
Immutability helps preserve the backup copy itself, but it does not replace restore testing, recovery planning, or validation of recovered data.
The next section explains why immutable backups matter more in healthcare than in many other industries.
How Immutable Backups Protect EHR Data and Patient Records
Preserving Trusted Restore Points for EHR Systems
EHR systems change constantly. Patient charts, appointments, orders, billing updates, and clinical notes are added throughout the day. If a ransomware event or system failure affects the environment, recovery depends on having a restore point that has not been changed or removed after backup creation.
Immutable backups help preserve that restore point in a fixed state for the defined retention period. This gives healthcare organizations a more reliable recovery reference when they need to bring systems back online.
Reducing Backup Tampering Risk
A backup can fail long before restore begins if the copy itself is deleted, encrypted, or altered. Immutability reduces that risk by limiting post-backup changes. This matters in healthcare because losing the backup layer can turn a system outage into a longer operational disruption.
That protection is especially important for systems tied to:
- EHR access
- patient record availability
- imaging workflows
- scheduling and billing operations
Supporting Recovery to a Known-Good Restore Point
The goal is not simply to restore data. The goal is to restore from a point the organization can trust. Immutable backups support that by helping preserve a stable copy that is less exposed to later changes inside the backup environment.
This improves recovery confidence, but it does not remove the need to confirm that restored data is usable. A protected copy still has to be validated once recovery starts.
Recovery Validation Still Matters After Backup Protection
Immutability protects the backup copy. It does not verify whether the restored data is complete, clean, and ready for operational use. Healthcare organizations still need to know whether recovered EHR data, patient records, and related systems can come back in a reliable state.
Preservation is the first step; validation is the final proof of recovery readiness.
This is why immutability is valuable, but not sufficient on its own. For organizations that need stronger recovery confidence, backup verification and recovery becomes just as important as preserving the backup copy itself.
The next section explains how immutable backups differ from regular backups and why that difference matters during recovery.
Immutable Backups vs Regular Backups in Healthcare
When healthcare organizations evaluate backup resilience, the key difference is not whether a backup exists. It is whether the restore point is still protected when recovery begins.
| Factor | Regular Backup | Immutable Backup |
| Core function | Creates a copy of data | Creates a copy of data and protects it from change for a defined retention period |
| Risk after backup creation | Backup copy may still be deleted, encrypted, overwritten, or altered | Backup copy is preserved in a fixed state during retention |
| Recovery confidence | Depends on whether the copy remained intact and usable | Stronger confidence that the restore point was preserved |
| Ransomware resilience | More exposed if attackers reach the backup environment | Better protected against post-backup tampering or deletion |
| Healthcare impact | May leave EHR, patient records, or operational systems without a dependable restore source | Helps preserve a known restore point for recovery |
| What it does not guarantee | Clean, complete, tested recovery | Clean, complete, tested recovery |
A regular backup can still fail the organization if the backup copy is compromised before recovery starts. An immutable backup reduces that risk by protecting the copy after it is created.
That difference matters in healthcare because backup completion is not the same as recovery readiness. A restore point can exist and still be unusable when the organization needs to bring EHR systems, scheduling, billing, or patient data back online.
Immutability improves backup protection, but healthcare organizations still need to verify that restored data is usable in practice.
The next section explains whether immutable backups alone are enough for ransomware recovery.
Are Immutable Backups Enough for Ransomware Recovery in Healthcare?
Limits of Immutable Backups in Ransomware Recovery
Immutable backups strengthen recovery protection, but they do not solve every recovery problem on their own. They help preserve the backup copy after it is created. They do not confirm that the restored data is complete, clean, or ready for operational use.
What Immutable Backups Protect
They reduce the risk of backup copies being deleted, overwritten, or altered during the retention period. In a ransomware event, that can make the difference between having a preserved restore point and discovering that the backup layer was compromised along with the production environment.
What Immutable Backups Do Not Guarantee
They do not fix weak recovery procedures, poor retention planning, compromised credentials, or untested restores. They also do not guarantee that recovered EHR data, patient records, or related systems will come back in a state the organization can trust.
Recovery Requirements Beyond Immutable Storage
Healthcare recovery still depends on restore testing, validation of recovered data, access controls, and a recovery process that reflects how clinical and administrative systems actually operate. Without that, an organization may preserve a backup copy but still struggle to restore normal operations.
This is where recovery readiness becomes more important than backup status alone. For healthcare organizations that need to know whether protected backup copies can actually restore in a usable state, a broader healthcare data backup strategy matters.
The next section explains what healthcare organizations should look for when evaluating an immutable backup strategy.
What to Look for in an Immutable Backup Strategy for Healthcare
Protected Backup Copies
An immutable backup strategy should do more than create copies of data. It should preserve those copies in a fixed state for a defined retention period so they cannot be deleted, overwritten, or altered after backup creation. This is the first layer of protection, but it is not enough on its own.
Recovery Outside the Production Environment
Healthcare organizations need a backup design that keeps recovery data available even if the live environment is compromised. That matters for EHR systems, patient records, imaging workflows, scheduling platforms, and billing operations that depend on timely restoration.
Restore Testing and Recovery Validation
A protected backup copy is useful only if it can be restored in a usable state. Restore testing and recovery validation help confirm whether recovered data is intact, accessible, and reliable under real recovery conditions.
Auditability, Visibility and Recovery Trust
Healthcare recovery depends on more than storage controls. It also depends on clear logging, retention visibility, and confidence in the restore process. An effective immutable backup strategy should support detailed documentation and audit trails that demonstrate recovery steps can be followed consistently when systems need to be restored, helping organizations meet regulatory requirements such as HIPAA, HITRUST, or GDPR.
Fit for EHR and Healthcare-Critical Systems
Not every backup design supports the pace and sensitivity of healthcare operations. The strategy should align with the systems that matter most, especially those tied to patient data and daily continuity. A backup plan that looks strong on paper can still create risk if it does not support practical recovery for the systems staff use every day.
The next section explains how immutable backups fit into a broader healthcare recovery plan.
How Immutable Backups Fit Into a Healthcare Recovery Plan
One Layer of Healthcare Backup Architecture
Immutable backups are one part of a broader recovery design. They help preserve backup copies after creation, but recovery planning still depends on where backups are stored, how systems are prioritized, and how quickly critical data can be restored.
Support for Ransomware Recovery Readiness
In healthcare, ransomware recovery is not only about having copies of data. It is about keeping at least one restore point protected when the production environment or backup layer is targeted. Immutability helps strengthen that part of the plan by reducing the risk of backup tampering during the retention period.
Why Recovery Validation Still Matters
A preserved backup copy does not automatically mean a successful recovery. Healthcare organizations still need to know whether recovered data is intact, complete, and usable for EHR access, scheduling, billing, imaging, and other operational needs. This is why recovery planning should include validation, not just retention.
Connection to a Broader Healthcare Backup Strategy
Immutable backups work best when they support a larger healthcare data backup approach built around resilience, recovery confidence, and protection of critical systems.
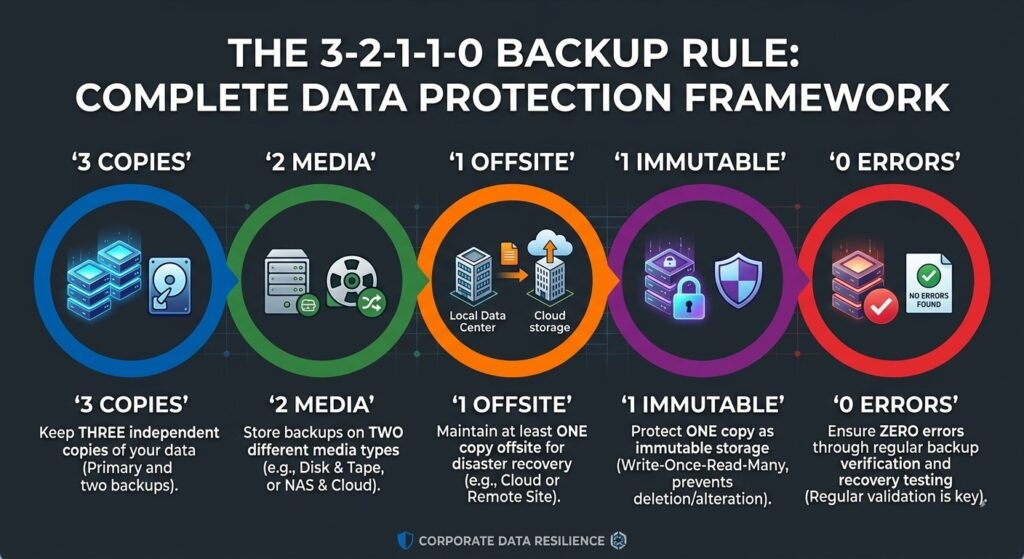
The 3-2-1-1-0 rule adds an extra layer of protection through immutability and verified recovery.
For organizations that also want to strengthen backup integrity after creation, the 3-2-1-1-0 backup rule for healthcare adds a useful framework around copy protection, isolation, and error-free recovery.
Immutable backups do not replace the recovery plan. They strengthen one of its most important layers.
Final Thoughts on Immutable Backups for Healthcare
Immutable backups help protect healthcare restore points from deletion, overwrite, and post-backup tampering. That makes them an important part of recovery planning, especially when ransomware or system failure puts EHR data, patient records, imaging, scheduling, billing, and other operational systems at risk.
But preserving a backup copy is only part of the recovery picture. Healthcare organizations still need to know whether restored data is usable, whether recovery steps have been tested, and whether critical systems can come back in a reliable state. That is where backup protection and recovery confidence need to work together.
If your team is reviewing backup resilience, Central Data Storage (CDS) can help you look beyond backup retention alone. A broader healthcare data backup strategy matters more than any single storage control. And if the bigger question is whether a restore point can be trusted after corruption, ransomware, or hidden failure, backup verification and recovery is where that evaluation becomes practical.
Healthcare Immutable Backups FAQs
Can immutable backups help healthcare organizations recover from insider mistakes?
Yes. Immutable backups help healthcare organizations recover from accidental deletion, overwrite, or unauthorized changes. Immutable storage preserves the backup copy, while recovery restores a trusted version of critical healthcare data.
Do immutable backups support healthcare business continuity?
Yes. Immutable backups support healthcare business continuity by preserving restore points during cyber incidents or system failure. Protected backup copies help recovery teams restore critical systems with less disruption to operations.
Are immutable backups useful for small medical and dental practices?
Yes. Immutable backups help small medical and dental practices protect patient data, reduce ransomware risk, and improve recovery confidence. Small practices need dependable restore points because they often have fewer internal recovery resources.
Can an immutable backup strategy reduce backup deletion risk?
Yes. An immutable backup strategy reduces backup deletion risk by locking backup copies for a defined retention period. Retention controls protect recovery data from deletion, overwrite, or unauthorized modification after backup creation.
Do immutable backups replace offsite healthcare backups?
No. Immutable backups do not replace offsite backups. Immutability protects the backup copy from change, while offsite backup protects recovery data from local outages, infrastructure failure, theft, or site-level disruption.
Can immutable backups support healthcare audit readiness?
Yes. Immutable backups support healthcare audit readiness when the backup platform provides retention visibility, restore records, and recovery documentation. Protected backup copies strengthen evidence that recovery controls are in place.
Last updated on April 14, 2026