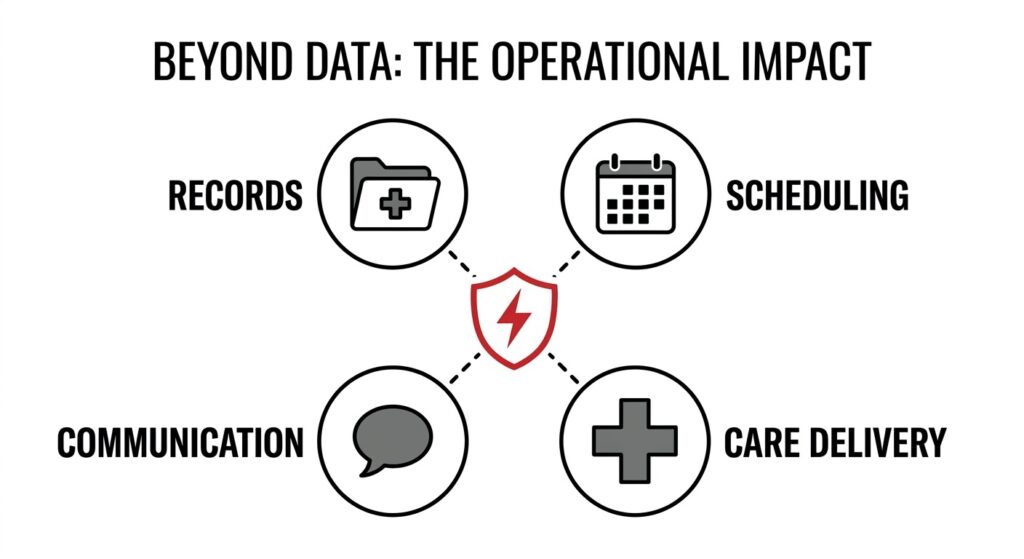
Iran-linked ransomware activity is a warning for healthcare providers because ransomware in healthcare can disrupt patient records, scheduling, communication, and care delivery, not just data access. When a provider loses access to critical systems, the impact quickly becomes operational. That is why healthcare organizations need more than prevention. They need recovery readiness.
A recent report from Cybersecurity Dive said an Iran-linked ransomware operation targeted U.S. organizations, including a healthcare provider, and tied the activity to Pay2Key. The report also cited concern that the campaign may be aimed at disruption, not only extortion. That matters in a sector where downtime creates immediate pressure on operations. [Source: Cybersecurity Dive]

With attacks occurring every 10 hours, the question is when, not if, a disruption will occur.
That warning fits a larger pattern. A Morningstar/Business Wire report, citing Securin, said healthcare faces a cyberattack every 10 hours, driven by known flaws and high ransomware payouts. [Source: Morningstar / Business Wire]
For healthcare providers, the takeaway is straightforward: the real question is not only how to reduce attack risk, but how to restore operations when disruption happens.
What Happened in the Iran-Linked Ransomware Attack on a U.S. Healthcare Provider?
According to Cybersecurity Dive, an Iran-linked ransomware operation targeted U.S. organizations, including a healthcare provider. The activity was associated with Pay2Key, and researchers raised concerns that the operation could be more disruptive than a standard extortion campaign.
This matters because healthcare remains a high-pressure target. Providers depend on always-available systems for chart access, patient coordination, scheduling, communication, and daily clinical workflows. When those systems are interrupted, the business impact quickly moves beyond IT.
A Halcyon report notes that attackers lurked in networks for days before launching ransomware and encrypting systems in about three hours. That compressed timeline increases the importance of restore planning, clean recovery points, and clear decision-making during an outage. [Source: Halcyon]
| Reported point | Why it matters to healthcare providers |
| A healthcare provider was among the targets | Healthcare remains exposed to ransomware-driven disruption |
| The operation was linked to Pay2Key | This fits a broader threat pattern, not a one-off event |
| Researchers flagged disruptive intent | Downtime may be the main business risk, not only ransom demand |
| Encryption reportedly moved quickly after deployment | Recovery readiness needs to be tested before an incident |
This incident is important not because it is unusual, but because it reflects how vulnerable healthcare operations become when core systems are unavailable.
Why Do Healthcare Providers Face Higher Ransomware Disruption Risk?
Ransomware impacts every facet of healthcare operations, moving quickly from a data issue to a patient care crisis.
Healthcare providers should pay attention because ransomware in healthcare can interrupt operations that support patient care. The damage is not limited to locked files. It can affect records access, appointment flow, communications, and coordination across the organization.
Healthcare carries more downtime pressure than most industries. Hospitals, clinics, specialty practices, and healthcare networks rely on connected environments that have to remain available throughout the day. That includes EHR access, patient management platforms, scheduling systems, specialty applications, and vendor-connected services.
| Healthcare dependency | Operational impact of disruption |
| Electronic health records | Delayed information access and slower clinical workflows |
| Scheduling systems | Appointment disruption and coordination issues |
| Internal communications | Slower escalation and incident handling |
| Specialty software and vendor platforms | Broader operational exposure across the environment |
This is also why healthcare cyber risk cannot be treated as a narrow security issue. In practice, it becomes a continuity issue. Providers that depend on patient management software or specialty platforms such as Open Dental backup support are especially exposed when an outage affects patient-facing operations.
The broader warning is simple: if a healthcare organization cannot restore systems in the right order and under real downtime pressure, the operational impact escalates fast.
What Does This Ransomware Incident Reveal About Healthcare Recovery Gaps?
This incident shows that healthcare providers need more than preventive controls. They need a recovery plan that restores critical systems quickly, uses clean restore points, and keeps operations moving while core platforms are unavailable.
A provider can have backups and still struggle during a ransomware event. The real issue is whether backup data is usable, whether recovery points are clean, and whether teams know what to restore first.
| Recovery area | Why it matters |
| Backup integrity | Corrupt or incomplete data can delay restoration |
| Restore order | Critical systems need to come back first |
| Downtime process | Teams need a workable plan while systems are unavailable |
| Recovery testing | Untested restores create risk during live disruption |
That gap between backup status and actual recoverability is common in healthcare. A completed backup job does not guarantee a clean, fast restore under pressure. This is the same issue reflected in CDS’s resource on why backup success fails in healthcare.
Healthcare recovery is also more complex than file restoration. Restoring data alone does not solve the problem if EHR access, scheduling, communications, or specialty workflows remain down. Recovery planning works better when teams know which systems must return first, which restore points are safe to use, and how long workflows can continue in downtime mode. That is why clean recovery matters, especially in environments where infected or unreliable restore points can slow recovery at the worst time. CDS addresses that directly in its article on clean vs. infected restore points in healthcare.
Infrastructure choices matter too. A provider with cloud-hosted systems, on-prem platforms, and vendor-connected tools will not recover the same way as a simpler environment. That is why recovery planning should match the environment being protected, including decisions around on-prem vs. cloud backup for EHR systems.
What Should Healthcare Organizations Review to Improve Recovery Readiness?
Healthcare organizations should review whether critical systems can be restored quickly, whether backup data is clean, and whether teams know how to operate during downtime.
Many organizations know what they back up, but not what they would restore first. In healthcare, restoring order matters because some systems directly affect patient care and daily operations, while others can wait.

Effective recovery requires a predetermined order of operations to restore critical care systems first.
| Review area | What to confirm |
| Critical systems | Which platforms must return first to support care and operations |
| Restore sequence | The order for EHR, scheduling, communications, and specialty tools |
| Recovery ownership | Who makes restore decisions during an active incident |
| Downtime threshold | How long each workflow can function without its main system |
Backup quality matters as much as backup availability. Restore points need to be recent, usable, and tested often enough to support a live recovery event. That is especially important in healthcare, where ransomware may remain undetected before disruption begins. CDS covers the practical issue of how often healthcare providers should test backup restores.
Organizations should also review what happens while systems are unavailable. That includes patient communication, scheduling workarounds, documentation procedures, and coordination between teams until systems return. A recovery plan is stronger when it supports both restoration and temporary operations. That is what turns backup planning into business continuity.
How Does CDS Help Healthcare Providers Improve Recovery Readiness?
Central Data Storage (CDS) helps healthcare providers reduce the impact of ransomware-related disruption by focusing on recoverability. That means protecting critical data, validating that recovery points are usable, and supporting faster restoration of essential systems after an outage.
Many organizations know backups are running, but that does not always answer the most important question during an incident: can the environment be restored cleanly and in the right order? CDS helps close that gap through backup verification and recovery, which fits naturally here because the main risk in events like this is not only data loss. It is a delayed recovery.
For providers, ransomware affects more than stored files. It can interrupt patient records, scheduling, communication, and practice workflows. That is why healthcare data recovery is relevant in this context. The challenge is restoring operational continuity, not only preserving data.
CDS also supports healthcare-specific environments through its healthcare data protection solutions, including support for platforms used by specialty practices and regulated healthcare organizations. For providers reviewing whether their environment is actually recoverable under pressure, a data assessment is the clearest next step.
If your organization is reviewing how it would respond to a ransomware-related outage, CDS can help you evaluate backup integrity, restore readiness, and healthcare recovery planning before disruption forces those decisions in real time.
Key Takeaways for Healthcare Providers From This Ransomware Threat
Iran-linked ransomware activity is a warning for healthcare providers because it highlights a persistent truth about cyber risk in healthcare: the real damage often comes from downtime. Providers that rely on digital systems for records, scheduling, communication, and care delivery cannot treat recovery as an afterthought. They need clean restore points, a clear recovery order, tested downtime procedures, and a realistic plan for maintaining operations when systems are unavailable.
That is what turns awareness into preparedness.
Additional Questions Matter for Healthcare Ransomware Preparedness
What is the first system a healthcare provider should restore after a ransomware attack?
Restore the EHR, scheduling, and communication systems first because those systems support patient care, coordination, and operational continuity.
How often should healthcare providers test ransomware recovery?
Healthcare providers should test ransomware recovery at least quarterly because regular testing validates backup integrity, restore speed, and downtime readiness.
What is an immutable backup in healthcare ransomware recovery?
An immutable backup protects healthcare data from deletion or encryption because the backup remains unchanged for a defined retention period.
How do RTO and RPO affect healthcare recovery planning?
RTO defines how fast healthcare systems must return, and RPO defines how much data loss is acceptable during recovery.
Why should healthcare providers assess vendor risk after a ransomware warning?
Healthcare providers should assess vendor risk because third-party platforms, EHR tools, and connected services can expand downtime and delay recovery.
Last updated on April 17, 2026