How Protecting Your Data Impacts Business Continuity?
Business continuity depends on consistent access to operational data, applications, and systems. When critical information becomes unavailable, organizations cannot operate normally.
Data protection, backup systems, and disaster recovery infrastructure maintain business continuity by ensuring that data remains recoverable during disruptions such as cyber attacks, infrastructure failures, or accidental data loss.
Organizations that protect operational data maintain the ability to:
- restore systems after outages
- recover critical records
- maintain service availability
- reduce operational downtime
Data protection forms the technical foundation that allows organizations to continue operations during unexpected events.
Why is Data Protection Essential for Business Continuity?
Modern organizations rely heavily on operational data. Examples include:
| Business Function | Data Required | Impact if Lost |
| Patient management | electronic health records | medical services disrupted |
| Financial systems | transaction databases | payment failures |
| Customer operations | CRM platforms | service interruptions |
| Logistics systems | inventory data | supply chain disruption |
When operational data becomes unavailable:
- applications stop functioning
- employees lose access to systems
- automated processes fail
- customers cannot access services
Maintaining recoverable data ensures operations resume quickly after incidents.
What is Business Continuity Planning (BCP)?
Business Continuity Planning (BCP) defines how an organization continues operating during disruptive events. BCP identifies:
- critical operational systems
- acceptable downtime limits
- data recovery requirements
- restoration procedures
The goal of business continuity planning is maintaining operational availability even when systems fail.
Core Components of Business Continuity Planning
| Component | Function | Result |
| Risk assessment | identify threats | operational awareness |
| Business impact analysis | determine critical systems | recovery priorities |
| Data protection | preserve recoverable data | prevent permanent loss |
| Disaster recovery | restore infrastructure | resume services |
| Recovery testing | verify restoration | reliable recovery |
These elements support the ability to restore systems after disruption.
Business Continuity vs Disaster Recovery
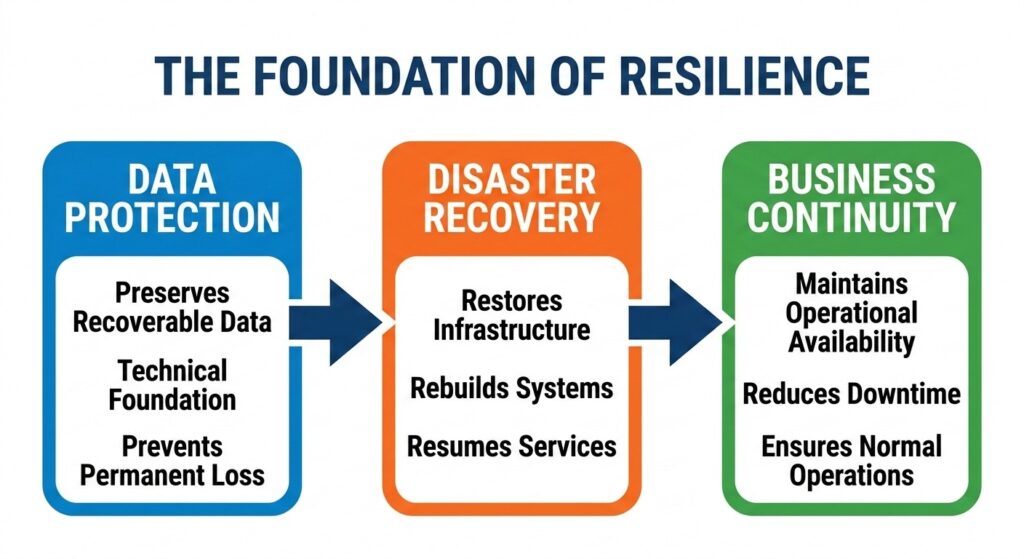
Data protection serves as the technical foundation for the entire continuity process.
Relationship:
Data Protection → Disaster Recovery → Business Continuity
Without protected data, disaster recovery cannot restore systems.
Recovery Time Objective (RTO) and Recovery Point Objective (RPO)

Understanding your RTO and RPO is vital for setting recovery expectations.
| Metric | Meaning |
| Recovery Time Objective (RTO) | maximum acceptable downtime |
| Recovery Point Objective (RPO) | maximum acceptable data loss |
Example recovery expectations:
| System | Typical RTO | Typical RPO |
| electronic health records | minutes | near-zero data loss |
| financial systems | minutes–hours | minimal transaction loss |
| CRM systems | hours | limited data loss |
These metrics determine how frequently backups run and how quickly systems must be restored.
Threats That Disrupt Business Continuity
Operational disruptions occur when systems, infrastructure, or data become unavailable. Common causes include cyber attacks, infrastructure failures, human error and natural disasters.
Each threat affects data availability, which determines whether operations continue. Lets find out more in detail:
1. Cyber Attacks and Ransomware
Ransomware encrypts operational systems and blocks access to data.
Affected systems may include:
- electronic health records
- file storage environments
- application databases
- authentication systems
Attackers often target backup systems to prevent recovery.
Protection methods include:
- isolated backup storage
- immutable backups
- verified recovery points
2. Infrastructure Failures
| Infrastructure Component | Result |
| server failure | application downtime |
| storage failure | data inaccessible |
| network outage | services unavailable |
| virtualization host failure | multiple systems offline |
Data protection systems allow organizations to restore systems onto new infrastructure.
3. Human Error
Examples include: accidental deletion, database misconfiguration and incorrect system updates.
Versioned backups restore earlier data states and recover lost information.
4. Natural Disasters
Environmental events can damage infrastructure. Examples include floods, fires and earthquakes
Offsite backups ensure that data remains available even if the primary facility is lost.
How Data Protection Ensures Operational Resilience?
Data protection ensures that recoverable copies of operational data exist when systems fail.
| Technology | Function |
| backup systems | preserve historical data copies |
| replication | duplicate data across systems |
| offsite storage | protect against site loss |
| immutable storage | protect against ransomware |
These mechanisms maintain recoverable data across multiple environments.
Backup and Disaster Recovery Strategies
Backup protects data.
Disaster recovery restores systems using that data.
Protected Data → Backup Storage → Disaster Recovery Restoration
Organizations design recovery architectures to meet RTO and RPO requirements.
Backup Architectures
| Backup Type | Purpose |
| full backup | restore complete system |
| incremental backup | store changed data |
| differential backup | store changes since last full backup |
| continuous data protection | capture real-time data changes |
Frequent backups reduce potential data loss during incidents.
Disaster Recovery Infrastructure
Typical recovery infrastructure includes:
- standby infrastructure
- cloud recovery environments
- virtual machine replicas
- secondary data centers
Recovery process:
| Step | Action |
| Step 1 | retrieve backup data |
| Step 2 | rebuild infrastructure |
| Step 3 | restore application databases |
| Step 4 | reconnect services |
| Step 5 | verify operations |
Why Backup Systems Sometimes Fail During Recovery?
Many healthcare providers assume their backups are safe until a restore attempt fails. Understanding why backup success does not always mean recoverability is critical for operational resilience.
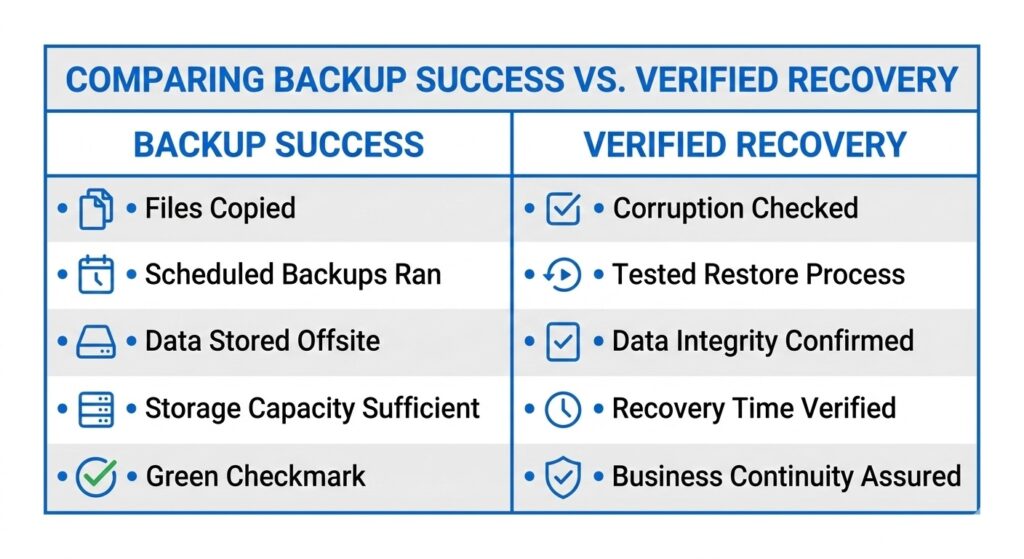
Verification is the difference between a backup that looks good and one that actually works.
Common causes of backup failure include:
- corrupted backup files
- incomplete backup chains
- ransomware-infected restore points
- untested recovery procedures
That analysis shows how backups that appear successful may still fail during restoration due to hidden data corruption or compromised backup sets.
Backup Verification and Disaster Recovery Practices
Reliable recovery requires validation of backup data.
| Validation Method | Purpose |
| integrity verification | detect corrupted backups |
| database validation | confirm data consistency |
| restore simulations | verify recovery capability |
| chain verification | confirm backup sequence continuity |
Backup systems must be tested regularly to ensure that restore points remain usable when systems fail or ransomware strikes.
The 3-2-1 Backup Model
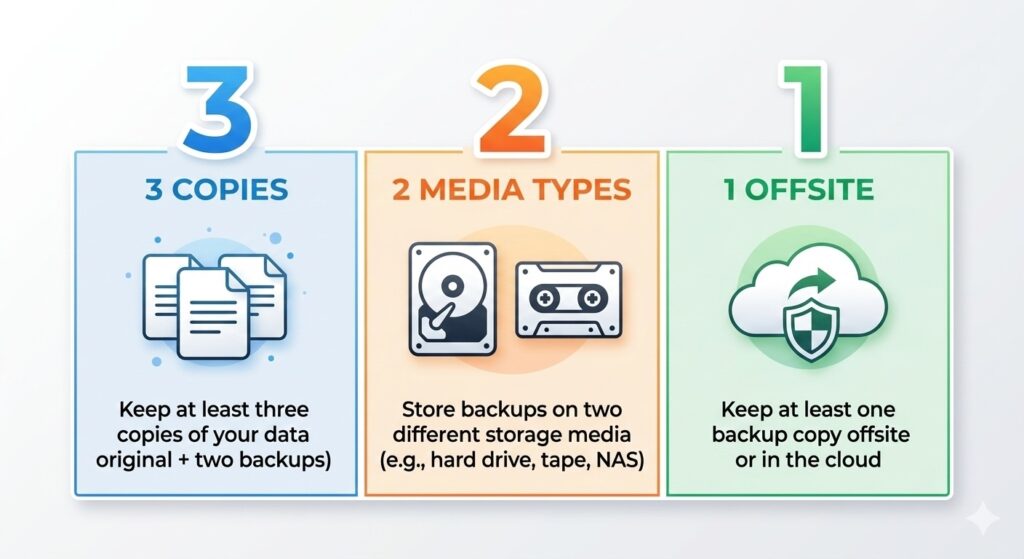
The 3-2-1 rule ensures that no single point of failure can destroy your data.
The 3-2-1 rule protects data by maintaining multiple copies.
Requirements:
- 3 copies of data
- 2 different storage systems
- 1 offsite backup location
Example deployment:
| Copy | Location | Purpose |
| primary data | production environment | operational use |
| local backup | internal storage | fast recovery |
| offsite backup | remote storage | disaster recovery |
Additional disaster recovery planning practices appear in the CDS resource Backup and Disaster Recovery Tips.
How CDS Backup Platforms Support Business Continuity
Central Data Storage (CDS) focuses on verified recovery infrastructure, ensuring that backup data can be restored during system failures or cyber incidents.
The CDS Unison platform provides multiple deployment models designed for different operational environments.
1. Unison Lite
Unison Lite provides managed backup environments for organizations without dedicated IT teams.
Capabilities include:
- automated encrypted backups
- monitored offsite storage
- assisted recovery operations
Common users include:
- dental practices
- small medical clinics
- legal offices
- professional service businesses
2. UnisonBDR
UnisonBDR provides full business continuity and disaster recovery infrastructure.
Capabilities include:
- orchestrated backup management
- ransomware-resistant storage
- restore validation
- automated recovery workflows
Deployment options include:
- managed infrastructure
- private deployments
- hybrid recovery environments
3. Unison Complete
Unison Complete combines on-site backup systems with offsite replication. Architecture includes:
- local backup appliances
- secure cloud replication
- disaster recovery orchestration
Local recovery enables rapid restoration, while remote copies protect against infrastructure loss.
Choosing the Right CDS Platform for your Organization
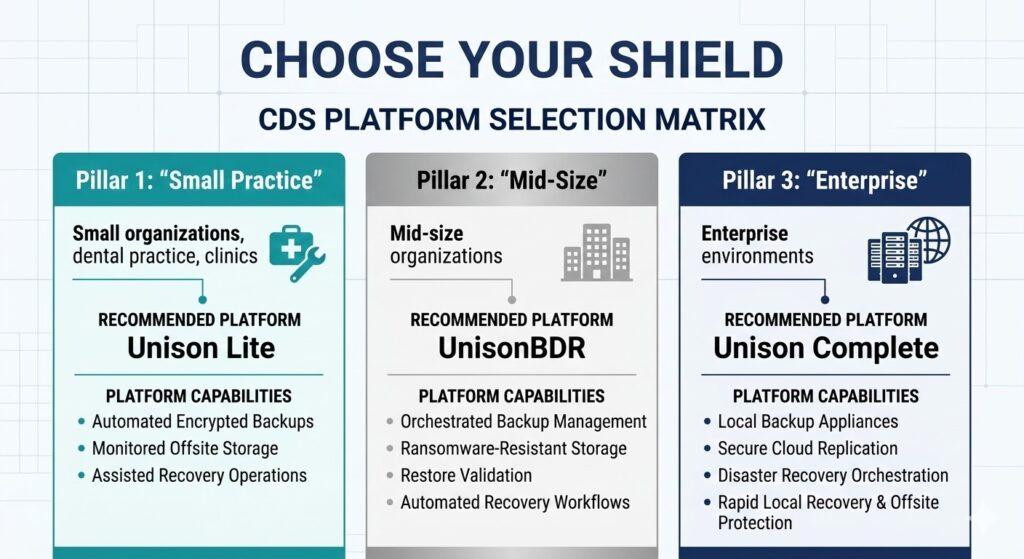
Choosing the right platform ensures your recovery capability matches your operational complexity.
Each platform prioritizes verified recovery rather than backup storage alone.
Request a Data Risk and Recovery Assessment
Organizations that depend on operational data should periodically evaluate their backup and recovery readiness.
Central Data Storage provides assessments that review:
- backup architecture
- recovery readiness
- ransomware resilience
- disaster recovery capability
Request a Data Risk & Recovery Assessment to determine whether your current backup system can restore operations during real incidents.
Data Protection and Business Continuity FAQs
What is the difference between data resilience and business continuity?
Data resilience protects data availability through backup, replication, and recovery. Business continuity maintains operations during disruption. Data resilience supports business continuity by ensuring systems restore usable data after outages or cyberattacks.
How does immutable backup improve business continuity?
Immutable backup prevents modification or deletion of stored backup data. Organizations use immutable storage to protect recovery points from ransomware attacks. Immutable backup ensures clean data remains available for disaster recovery and business continuity.
What role does data classification play in business continuity planning?
Data classification identifies critical data assets based on sensitivity and operational importance. Organizations classify data to prioritize backup frequency, security controls, and recovery speed. Data classification improves business continuity by protecting the most critical information first.
What role does data classification play in business continuity planning?
Data classification identifies critical data assets based on sensitivity and operational importance. Organizations classify data to prioritize backup frequency, security controls, and recovery speed. Data classification improves business continuity by protecting the most critical information first.
How does network segmentation protect backup systems from ransomware?
Network segmentation isolates backup infrastructure from production systems. Security teams restrict network access to backup servers and storage environments. Network segmentation protects backup systems by preventing ransomware from spreading across infrastructure.
Last updated on March 9, 2026